| Developer(s) | Mike Kershaw (dragorn) |
|---|---|
| Stable release | 2020-04-R3[1] / May 2, 2020; 5 months ago |
| Repository | |
| Written in | C++ |
| Operating system | Cross-platform |
| Type | Packet Sniffer |
| License | GPL |
| Website | www.kismetwireless.net |
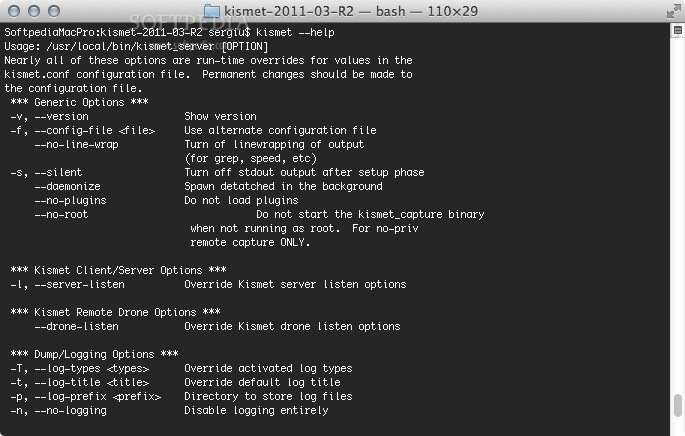
Figure 1 - Kismet UI. Finding out the MAC. In order to track somebody via wifi, you will need to get their MAC address one way or another. You can ask for it, or use social engineering to find it out (e.g. Ask to see their network settings in order to troubleshoot some made-up issue), or you will have to work for it in case you do not have. The kismetserver may be started as a daemon from the command line. This will make it available to client interactions and also start logging. No changes to the above configuration are needed. It is also possible to start kismetserver from boot but this is not my preference due to GPS Fix delays.
Kismet is a network detector, packet sniffer, and intrusion detection system for 802.11wireless LANs. Kismet will work with any wireless card which supports raw monitoring mode, and can sniff 802.11a, 802.11b, 802.11g, and 802.11n traffic. The program runs under Linux, FreeBSD, NetBSD, OpenBSD, and Mac OS X. The client can also run on Microsoft Windows, although, aside from external drones (see below), there's only one supported wireless hardware available as packet source.
Distributed under the GNU General Public License,[2] Kismet is free software.
Features[edit]
Kismet differs from other wireless network detectors in working passively. Namely, without sending any loggable packets, it is able to detect the presence of both wireless access points and wireless clients, and to associate them with each other. It is also the most widely used and up to date open source wireless monitoring tool.[citation needed]
Kismet also includes basic wireless IDS features such as detecting active wireless sniffing programs including NetStumbler, as well as a number of wireless network attacks.
Kismet features the ability to log all sniffed packets and save them in a tcpdump/Wireshark or Airsnort compatible file format. Kismet can also capture 'Per-Packet Information' headers.
Kismet also features the ability to detect default or 'not configured' networks, probe requests, and determine what level of wireless encryption is used on a given access point.
In order to find as many networks as possible, Kismet supports channel hopping. This means that it constantly changes from channel to channel non-sequentially, in a user-defined sequence with a default value that leaves big holes between channels (for example, 1-6-11-2-7-12-3-8-13-4-9-14-5-10). The advantage with this method is that it will capture more packets because adjacent channels overlap.
Kismet also supports logging of the geographical coordinates of the network if the input from a GPS receiver is additionally available.
Server / Drone / Client infrastructure[edit]
Kismet has three separate parts. A drone can be used to collect packets, and then pass them on to a server for interpretation. A server can either be used in conjunction with a drone, or on its own, interpreting packet data, and extrapolating wireless information, and organizing it. The client communicates with the server and displays the information the server collects.
Plugins[edit]
With the updating of Kismet to -ng, Kismet now supports a wide variety of scanning plugins including DECT, Bluetooth, and others.
Usage[edit]
Kismet is used in a number of commercial and open source projects. It is distributed with Kali Linux.[3] It is used for wireless reconnaissance,[4] and can be used with other packages for an inexpensive wireless intrusion detection system.[5] It has been used in a number of peer reviewed studies such as 'Detecting Rogue Access Points using Kismet'.[6]
See also[edit]
- KisMAC (for Mac OS X)
References[edit]
- ^https://www.kismetwireless.net/ Kismet web site
- ^'Kismet Readme'. kismetwireless.net. Retrieved 2008-02-22.
- ^'Kismet'. Kali Tools. Kali Linux.
- ^Lynn, Michael; Biondi, Philippe; Beauchesne, Nicolas (August 2007). Security Power Tools. O'Reilly Media. Retrieved 9 March 2016.
- ^Murray, Jason. 'An Inexpensive Wireless IDS using Kismet and OpenWRT'. SANS Institute. Retrieved 9 March 2016.
- ^Thejdeep, G. (2015). 'Detecting Rogue Access Points using Kismet'. In Communications and Signal Processing: 0172–0175. doi:10.1109/ICCSP.2015.7322813. ISBN978-1-4799-8081-9.
External links[edit]
Released:
Library for parsing kismet results from the .kismet database file.
Project description
This library can be used to analyze the results of the new Kismet version. To filter encryption types Kismet version 'f07735c' (Aug 19, 2018) or later is required.
The following scripts will be installed:
- kismet_analyzer_aplist: This script can be used to extract access points from the SQLite database <db>.kismet and export these results to csv and kml
- kismet_analyzer_clientlist This script can be used to create a list of connected clients for a given SSID. The list is printed to stdout with one client mac per row.
License
This script is licensed under the GNU General Public License in version 3. See http://www.gnu.org/licenses/ for further details.
Installation:
Installation via pip
Manual installation from this repository
This library requires simplekml for exporting extracted information to kml. You can use pip to install the neccessary requirement.
The setup script can be used to install the library and requirements. It will create the above listed console commands.
Usage:
Export only access points with encryption type 'Open' to csv and kml files:
Output example for kml exports
The script generates colored notes for exported access points. The color depends on the identified encryption type. WPA encrypted access points will be added with a green color, WEP encrypted networks will be displayed in orange and Open network are displayed in red. Networks were the encryption type could not be detected will be added as a yellow note. Each note contains detailed meta information about the access point (SSID, MAC address, frequency, channel, manufacturer, and a list of clients MAC addresses).
Release historyRelease notifications | RSS feed
0.3.1
0.3.0
0.2.1
Download files
Kismet For Mac Os
Download the file for your platform. If you're not sure which to choose, learn more about installing packages.
| Filename, size | File type | Python version | Upload date | Hashes |
|---|---|---|---|---|
| Filename, size kismet_analyzer-0.3.1-py3.8.egg (16.7 kB) | File type Egg | Python version 3.8 | Upload date | Hashes |
| Filename, size kismet_analyzer-0.3.1-py3-none-any.whl (8.9 kB) | File type Wheel | Python version py3 | Upload date | Hashes |
| Filename, size kismet-analyzer-0.3.1.tar.gz (7.3 kB) | File type Source | Python version None | Upload date | Hashes |
Hashes for kismet_analyzer-0.3.1-py3.8.egg
| Algorithm | Hash digest |
|---|---|
| SHA256 | 18380d4701ba7da6aa3c635318ba779150ea08ce301a477f247d9524ca9dd043 |
| MD5 | f99a31c6747c433ca3f692d2d6094812 |
| BLAKE2-256 | 500203a234615114e8b2889cc242550a01411b05018ee787f5bbb55b3d24965d |
Hashes for kismet_analyzer-0.3.1-py3-none-any.whl
| Algorithm | Hash digest |
|---|---|
| SHA256 | 5dc80392d3b626fccd6a595da3307837572f1f07eb882742c72db22a2dbd42c0 |
| MD5 | 91664aae33ce1eb72a4a30e8adb6544d |
| BLAKE2-256 | 58618f9b217338b46ae79980de72c1a6615b33aacfc71a2a5ba3b74b5748f467 |
Hashes for kismet-analyzer-0.3.1.tar.gz
Kismet Macquarie Park
| Algorithm | Hash digest |
|---|---|
| SHA256 | 859bb8ea4b42cd209c012db795518c0269e5033788b417594952ddf033f48587 |
| MD5 | 7286237b78fa6e5e15b627c29b80c7ff |
| BLAKE2-256 | ad000404a598b776e0a2fe7f20eb3d190d471701d07f782278d1a7f662855da4 |
